Protect your identity after a data breach or cyber-attack
The ACT Government supports people when they are the victim of a data breach or cyber-attack. We understand the concerns you have for the security of your personal information. When an incident occurs, we work with the relevant authorities to assess its scale. We’ll provide advice once it becomes available.
Personal information that may be exposed in a data breach or cyber-attack includes:
- customer names
- dates of birth
- contact details
- account login information
- unique numbers on identity documents.
Your right to know about a data breach or cyber-attack
If an organisation is involved in an incident, they must notify affected individuals. This includes telling people when their personal information has been accessed. An organisation has 30 days to consider if a data breach or cyber-attack has caused serious harm.
You may receive an email, text message or phone notification. Your notification should:
- contain the name of the organisation
- include what personal information was identified in the breach
- give you information about what happened in the incident
- provide you with advice on how to protect yourself in response
- give you contact details so you can seek further information.
You do not need to supply personal information when notified of an incident.
The OAIC provide further information on how data breaches and cyber-attacks get reported.
If you want to learn how the ACT Government keeps your information safe, you can read our privacy statement.
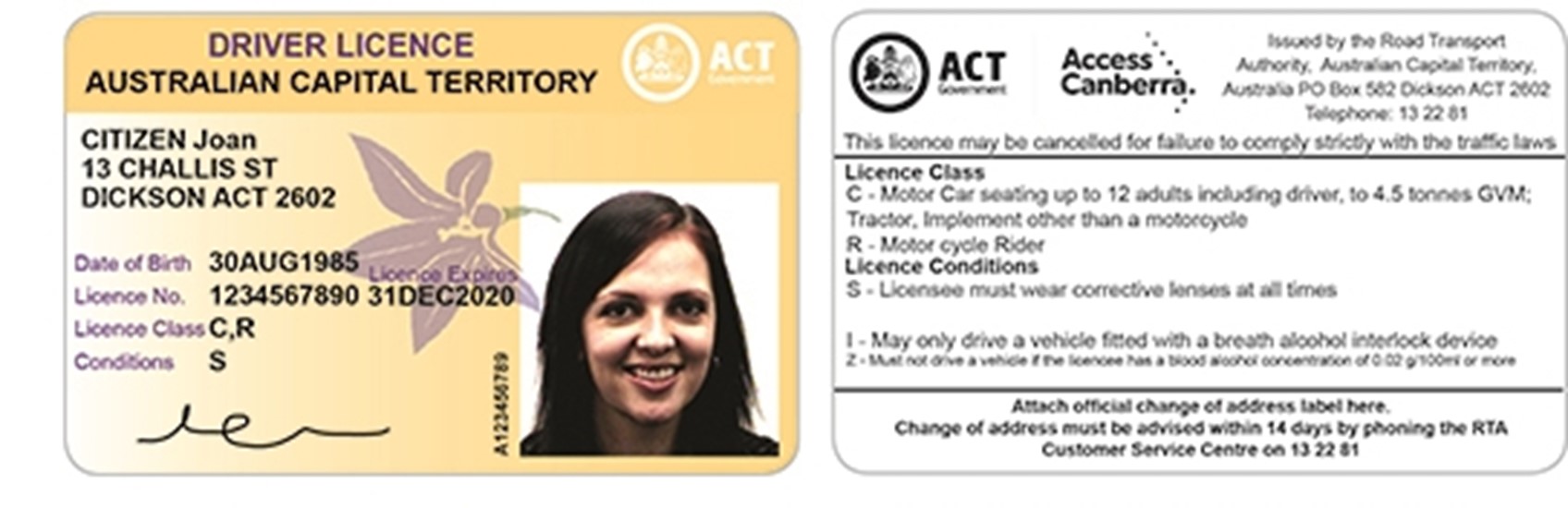
My driver licence information has been exposed
Current identity verification systems use two separate fields to verify your identity. These fields are your;
- driver licence number
- driver licence card number.
The numbers are located on your driver licence card as two separate numbers.
Your unique driver licence number:
- stays with you for life
- does not change when you receive new card.
Your driver licence card number:
- is a unique number printed vertically next to your licence photograph
- changes every time you receive a new card
- reduces the ability for this piece of identification to be used for fraud.
In a data breach or cyber-attack, you can be partially or fully compromised.
You are:
- partially compromised when only your driver licence number is exposed
- fully compromised when both your driver licence number and driver licence card number are exposed.
Verifying your identity using a driver licence
Your identity needs to be verified when you apply for financial products or connect services such as mobile phone plans.
To successfully verify your identity, you must supply your:
- driver licence number
- driver licence card number.
Verification will fail if you do not supply both numbers. This security measure aims to improve identity protections for people living in the ACT.
Replace your driver licence
You may receive advice that your licence has been fully compromised. This advice will come from Access Canberra or the affected organisation. We strongly encourage you to replace your licence in this situation.
To replace your driver licence, you can:
- apply for your replacement driver licence online
- attend an Access Canberra Service Centre
- contact us on 13 22 81.
When you replace your ACT driver licence, you will receive a new driver licence card number. This protects you from Document Verification Service (DVS) checks using the old card’s information. Institutions such as banks use a DVS check to verify a person’s identity.
Your driver licence number is not changed when you replace your driver licence.
Change your driver licence number
You can only change your driver licence number in very limited circumstances. This only happens when there is evidence of actual fraud or identity theft. Examples of fraud or identity theft include:
- opening a bank account or establishing a new mobile phone service
- falsely accessing government benefits
- avoiding licence bans or allocating fines and demerit points.
My information is part of a data breach or cyber-attack
To protect yourself following a data breach or cyber-attack, you can:
- review your online accounts for unexpected changes or suspicious activity
- check your services and bank accounts for unauthorised transactions or charges
- report any fraudulent activity immediately to the organisation responsible
- be suspicious of unexpected contact from individuals claiming to be from a real organisation.
Scammers use your personal information to contact you by email, text messages, phone calls or through social media. They use techniques to pressure you into providing your personal information. People making an unsolicited call for a real organisation should never ask you for personal information. They will not pressure you to provide personal information.
Messages from scammers can look like they are coming from a real organisation. Ask yourself when opening emails or text messages if you contacted the organisation recently. If you did not, then treat the message as suspicious.
When you receive a suspicious email or text message:
- do not click on any links
- do not provide passwords or supply any personal information
- do not reply and delete the message immediately.
Check your account details
People may use your personal information to access accounts that you operate. In these situations, they may change information in your account. Check that vital account information has not changed.
Email accounts are especially vulnerable. Check that there are no changes to:
- your account profile
- personal settings
- login access restrictions
- account synchronisation settings or onforwarding rules
- recovery details for your email account.
Any unexpected changes in your accounts require immediate attention. Contact the relevant organisation to fix your account. Talk about applying extra security measures to better restrict access to your account.
Strengthen passwords for your online accounts
After scanning your devices for viruses, strengthen your online account passwords. You should prioritise strengthening passwords for:
- government services such as the ACT Government Digital Account or MyGov
- stand-alone and web-based email services such as Gmail or Hotmail
- telephone services, internet services or utilities (gas, electricity, water) accounts
- online shopping accounts you use regularly or contain saved personal information
- bank accounts you regularly access online.
Do not reuse passwords. Instead, you should use unique passwords or passphrases for each online account. The Australian Cyber Security Centre (ACSC) provides advice on managing your passwords.
Protect yourself online
Build your cyber security knowledge so you can protect yourself and loved ones. The Australian Cyber Security Centre (ACSC) provide the following guidance that can help build your awareness.
- ACSC Information for individuals and families.
- Visit the cyber security learning hub.
Other steps you can take
Completing these steps can provide you with further protection following an incident.
- Visit moneysmart.gov.au to find out how to request your credit score and history for free.
- Prevent credit reporting agencies from sharing your credit information by placing a ban on your credit report.
- Regularly scan your devices for viruses. The ACSC provide guidance on virus scanning.
- Ensure you keep device operating systems up to date. The ACSC provide advice on updating devices.
- Support is available via IDCARE, Australia’s national identity and cyber support service. You can contact IDCARE for free support on 1800 595 160 or visit idcare.org.